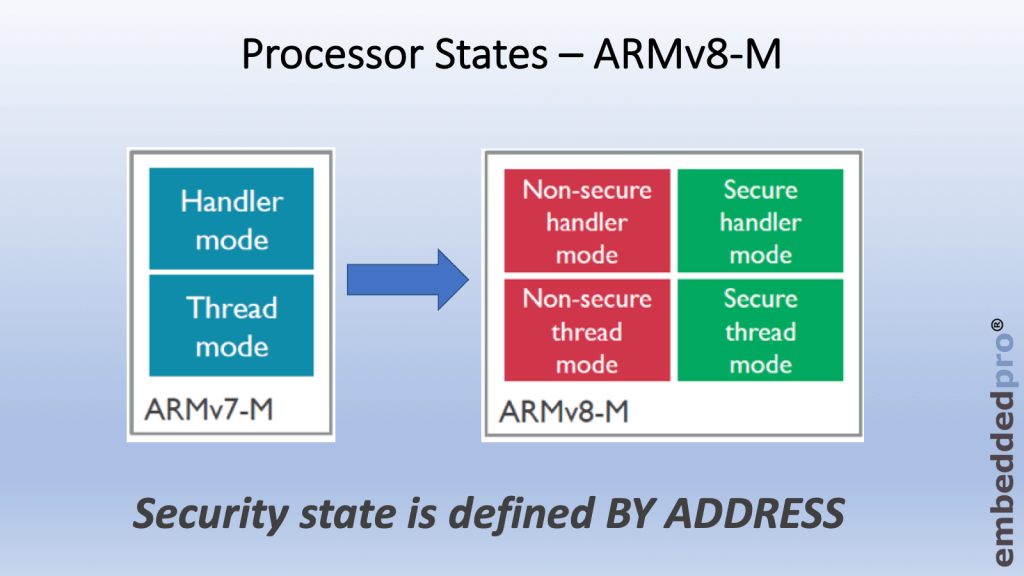
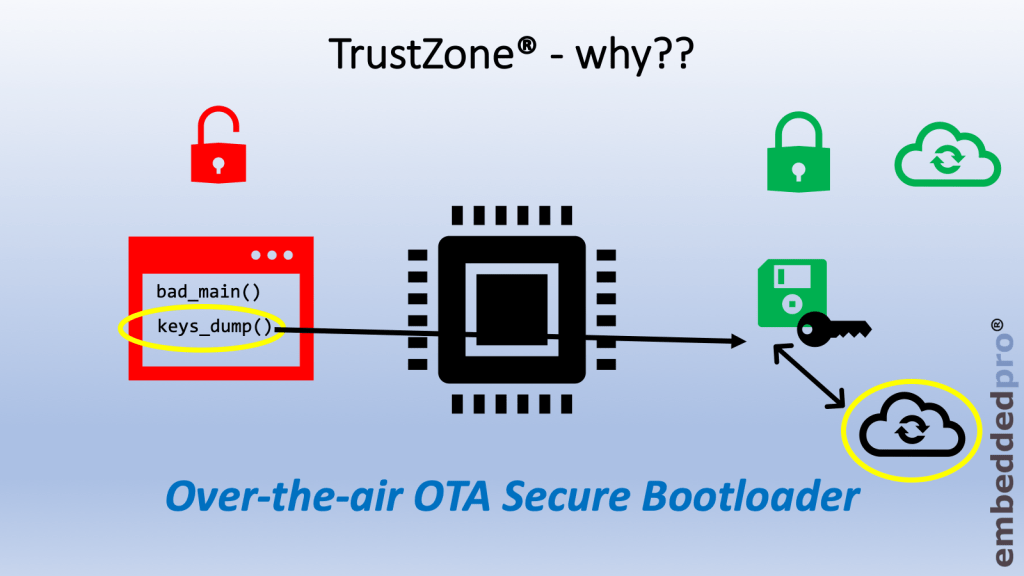
When we are learning about TrustZone® it does not take long to recognise that it is the security attributes for memory that define memory regions to be Secure, Non-Secure or Non-Secure Callable. This week’s video shows how the Cortex® M33 core with TrustZone® extension can test the security attributes for every read, write and execute from memory (without impacting performance). And how the security attributes are set with the Trusted Execution Environment configuration tool inside MCUXpresso IDE.