I spend a lot of my time writing software to run on manufacturers’ evaluation (or development) boards. Here on Erich’s site, my blogs have been based on Cortex M33, using NXP’s LPC55S69-EVK and LPC55S16-EVK. Development boards are great – firstly you know that the suppliers’ software should run without issues, and secondly: many of the pin functions are brought out to headers, transceivers, codecs, switches and LEDs. So, whilst it is easy to get started, by definition the boards can be large physically, power hungry, and expensive.
What do you do if you need to embed a high performance microcontroller into your prototype or small production run and don’t have time (or the inclination) to spin out a PCB?
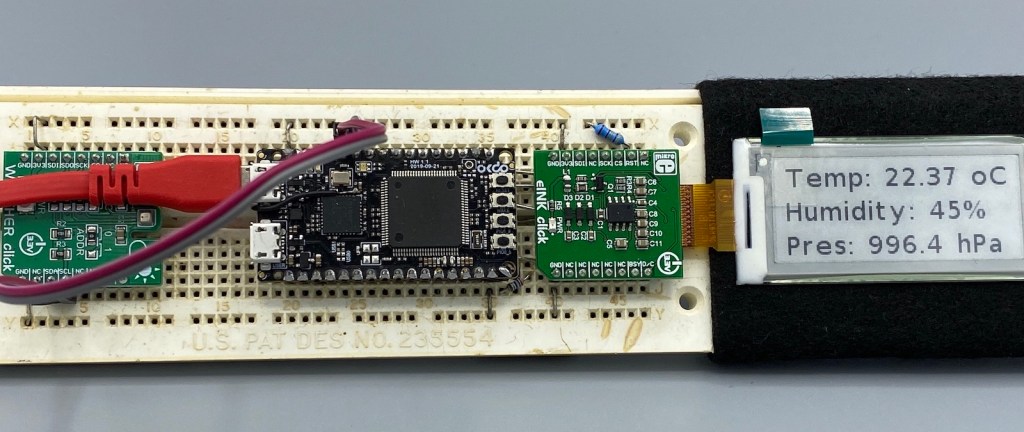
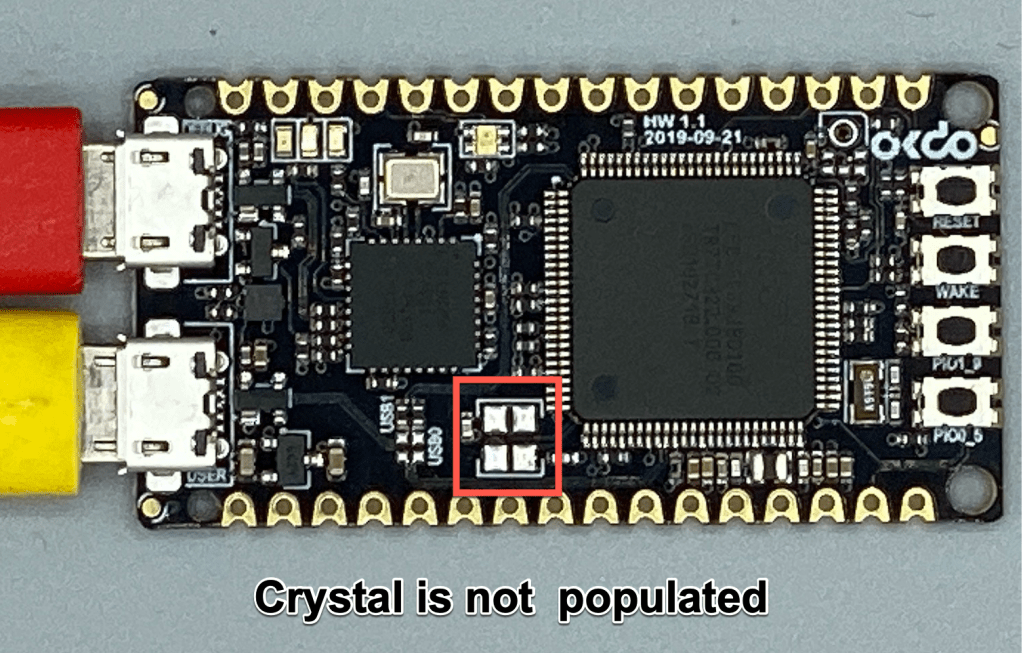
The answer is the OKdo E1 board, based on NXP’s LPC55S69 Cortex-M33 microcontroller.
Continue reading →