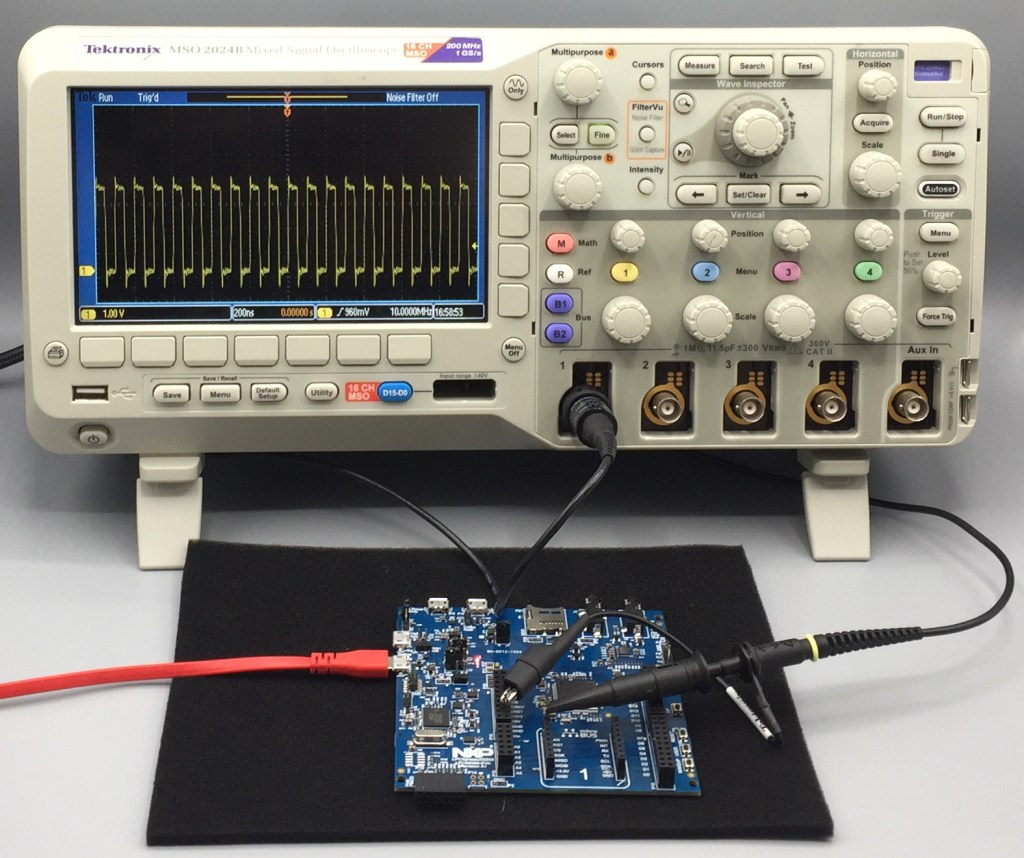
For this last blog in the series Investigating ARM Cortex® M33 core I decided to explore the expansion features of the LPC55S69-EVK. This board has three expansion ports (PMOD, Arduino Duo, Mikroe click) and I picked the Mikroe expansion port. Why? Only because I had good experience with these boards with the Hexiwear project.
And because I have been doing some work this month with AWS IOT I wanted to get my LPC55S69-EVK onto my office WiFi network for the Christmas holidays. I know that the MCUXpresso SDK for lpcxpresso55s69 version 2.6.3 has a built-in WiFi example named qca_demo, and so that is what I am investigating today.
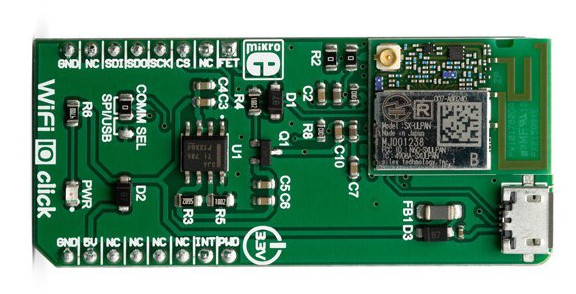
That WiFi example supports three WiFi shield boards, and I picked the Mikroe WiFi 10 click board. It’s part number MIKROE-3432 and available from all of the usual catalogue distributors.