From my previous MetaClockClock project, I still had some hardware available. So I decided to build my largest build so far: to clocks with 78 clocks each.


From my previous MetaClockClock project, I still had some hardware available. So I decided to build my largest build so far: to clocks with 78 clocks each.

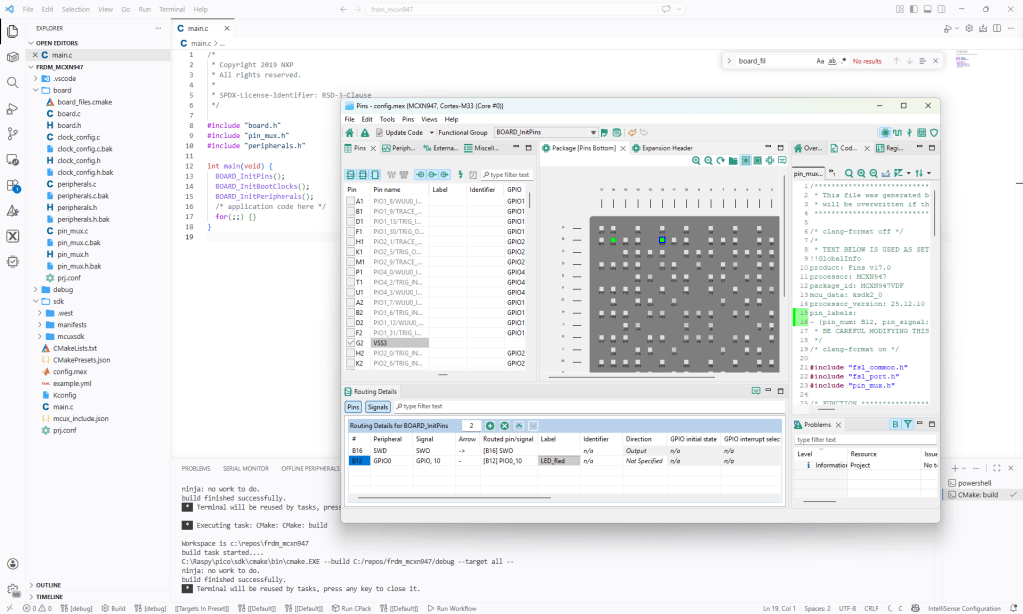
In Tutorial: Getting Started with MCUXpresso SDK – Repositories with VS Code and Tutorial: Getting Started with MCUXpresso SDK – west I showed how to get the MCUXpresso SDK. In this article it is about tweaking and streamlining the project.
The result is a clean, portable and self-contained MCUXpresso SDK project.
Recently I have been asked “How can I debug a Linux application with VS Code?”. I’m covering that topic in my ‘Embedded Application Development Course on Linux”.
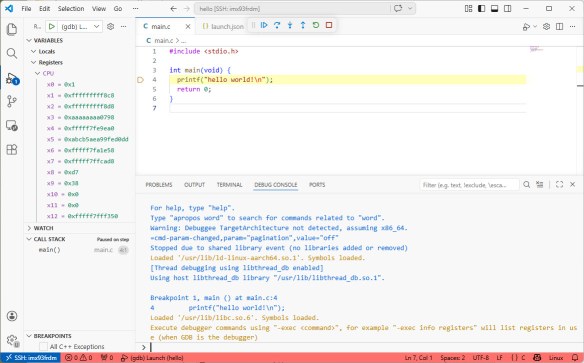
I realized, that I have never covered that topic in any of my blog articles. So here we go: I show how easy it is to use VS Code to debug a Linux application. You can use this for example with an Raspberry Pi. Or for example the NXP i.MX93 which I’m using in this article.
Continue readingIn “Tutorial: Getting Started with MCUXpresso SDK – west“, I demonstrated the ‘west’ tool’s usage. It helps in acquiring an SDK repository. Instead using the command line tool, I can use the NXP VS Code extension to do the same.
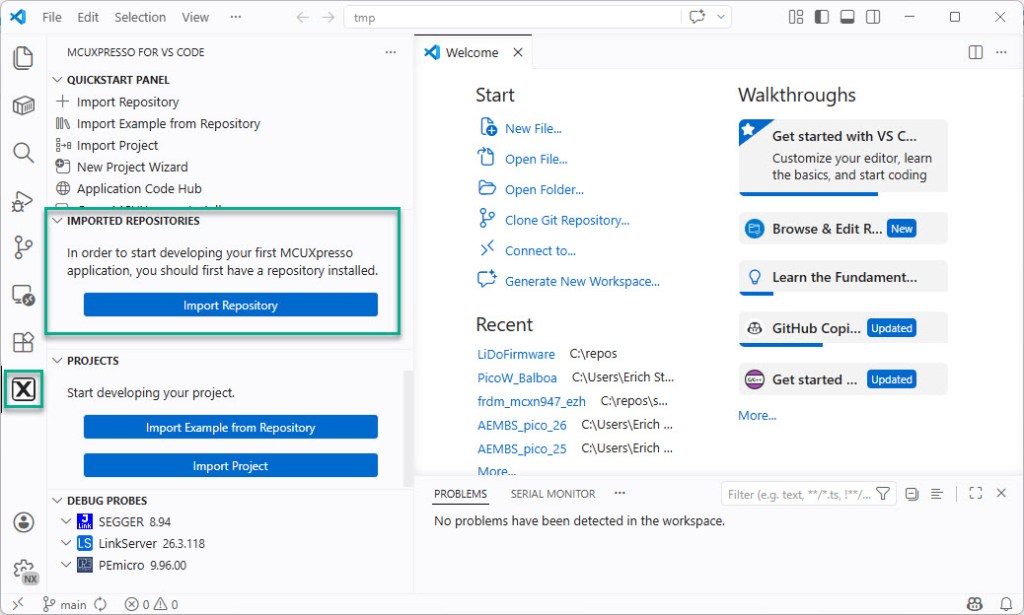
The engineering and development landscape is constantly changing. This includes the embedded tooling and SDKs.
Back in the year 2017 I have used the version 2 (see Tutorial: Using Eclipse with NXP MCUXpresso SDK v2 and Processor Expert). Back then, it was Eclipse with make. Now we are in 2026 and things have changed to VS Code, cmake, ninja, python and west.
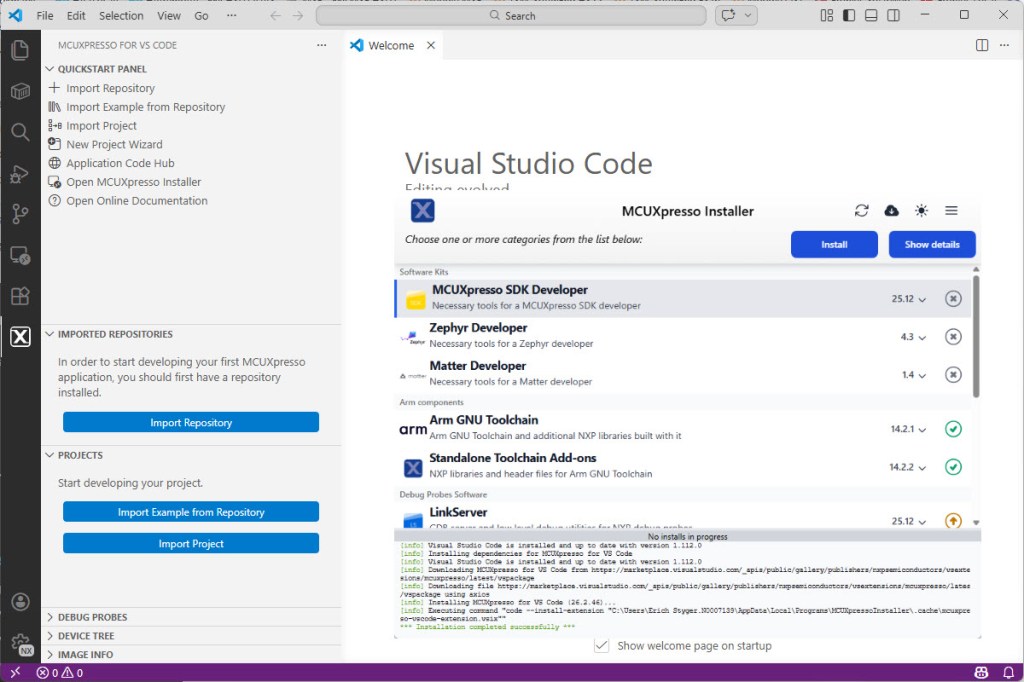
Luckily, although more and different tools are needed these days, the installation experience has improved significantly. It has shifted from installing multiple different tools to a streamlined installation process.
Continue readingThe latest release of the NXP LinkServer supports ARM 64bit (Debian) besides Windows, Linux and MacOS. With this, I can now develop on an NXP i.MX board. Plus, this enables an inexpensive way for automated on-target tests and CI/CD.
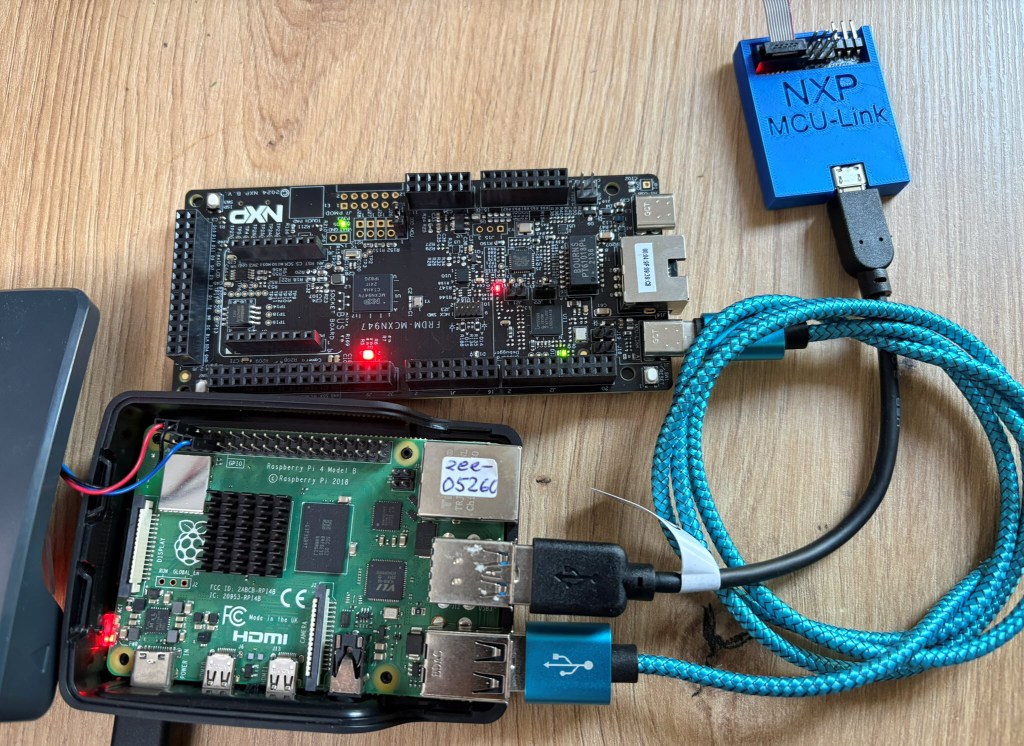
The new v0.5 MCU-Link-MR PCB (see MCU-Link-MR v0.5: Enhanced Debug Probe for ARM Cortex-M) comes with an extra pin header for logic analyzer signals. Because of this I have updated the enclosure for it:

A few days ago, a reader of my blog sent me a message:
“Hi Erich, I am reading you since a lot of years. I think you are a pillar of my professional career. Thanks for this. Let me ask you now: what do you think about LLM and coding with LLM in embedded? My employer thinks it time to stop to hire people, because in 1/2 years everything will be substituted by AI. I am not on the same page. Are you using LLM for coding? What do you think about it? Thanks in advance.”
TL;DR: LLMs are changing and improving, making good engineering and education even more important. Studies show that AI can be useful, but productivity will not always increase. AI coding means more critical thinking and responsibility, not less. Engineering and education needs to adopt and change. This includes assessments and didactic, back to paper and defending the work. Learning how to learn is getting the critical skill in the age of AI.
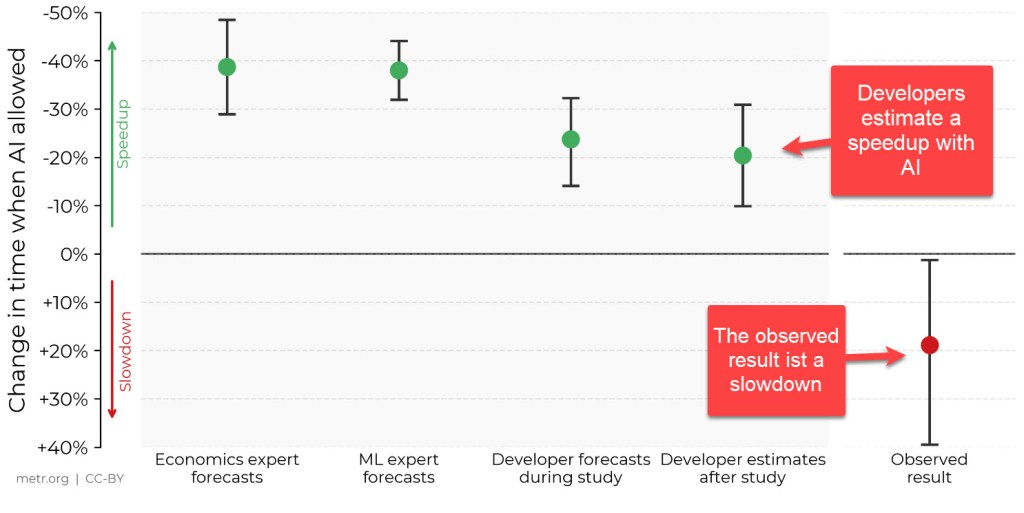
In this article I’ll have collected my thoughts and observations.
Continue readingThe MCU-Link-MR debug probe has been updated :-).

The MCU-Link-MR is a CMSIS-DAP debug probe for ARM Cortex-M devices with extra features for mobile robot and drone debugging. The project is open source and available on GitHub with KiCAD files and BOM.
Continue readingI’m using the NXP MCU-Link CMSIS-DAP debug probe in many of my projects. The debub probe from NXP does not come with an enclosure. I’m traveling to work by train, so I designed a new rugged box and enclosure. The box is small and I can keep all parts inside it.
