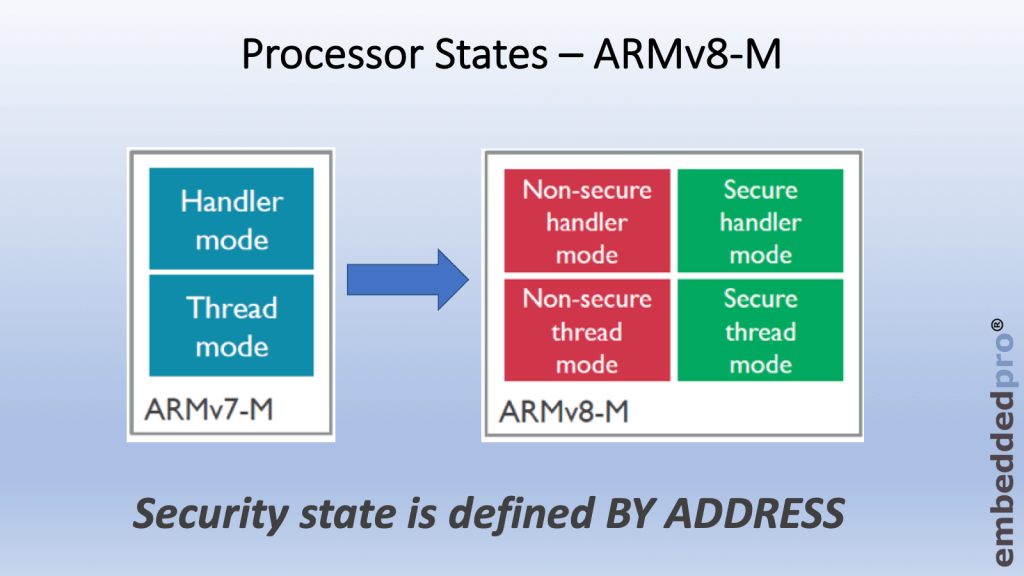
Last week I wrote about why we need the TrustZone® security extension for ARMv8-M. There are software use-cases where it can be very helpful to partition the software into 2 separate worlds, secure and non-secure. TrustZone® acts as the gatekeeper between these two worlds and manages how the core transitions between the worlds. The ARMv8-M architecture introduces two new States for the core – secure and non-secure. Cortex® M33 core (and M23 core also) is implemented to ARMv8-M standard and of course supports the two new states.
Erich blogged about TrustZone® and running projects in MCUXpresso IDE quite soon after the LPC55S69 was launched. That material can be found here and is essential background information. I recommend that you take a look. Please be aware that MCUXpresso IDE has been through a couple of revisions, and the way to load TrustZone® projects has improved since April 2019.
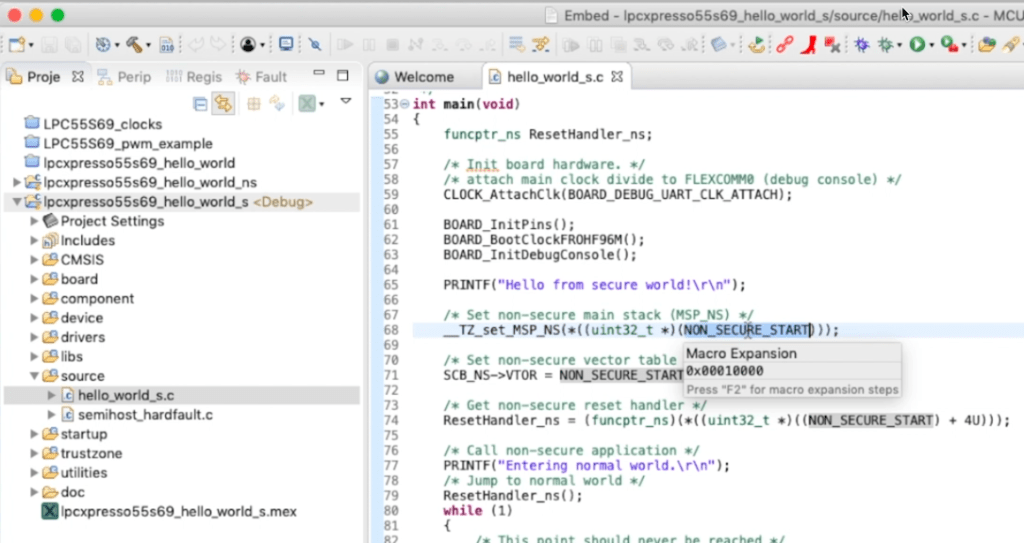
With the introduction of MCUXpresso IDE v11, the two TrustZone® projects can be downloaded to flash, and a debug session started simply by using the Quickstart panel ‘Debug’ feature to download the ‘secure’ project. The secure and non-secure projects are connected inside MCUXpresso and will both download to the LPC55S69-EVK.
This week in my video, after a short introduction about these new secure and non-secure states, we take a look at running the first TrustZone® examples from the MCUXpresso SDK. It is all straight-forward for those of us familiar with running the other SDK examples.
Feel free to head over to the embeddedpro® channel on YouTube, or you can watch the video embedded here. As always I am happy to hear your comments and feedback, and come back next week when I’ll blog about how the security attributes for memory in a TrustZone® project are configured with the Trusted Execution Environment tool.

Hi Mark,
can we use aarch64 inside the LPC55S69 ? I believe we can, but MCUXpresso seems to use an arm toolchain, but unsure how we can switch to aarch64 if supported by the LPC.
Thanks for the answer you would provide in that regard.
LikeLike
Hi Emmanuel, of course LPC55S69 is based upon ArmV8-M profile. The suffix -M is important. aarch64 is an extension to the ArmV8-A profile, and so is not possible to run on LPC55S69.
LikeLike