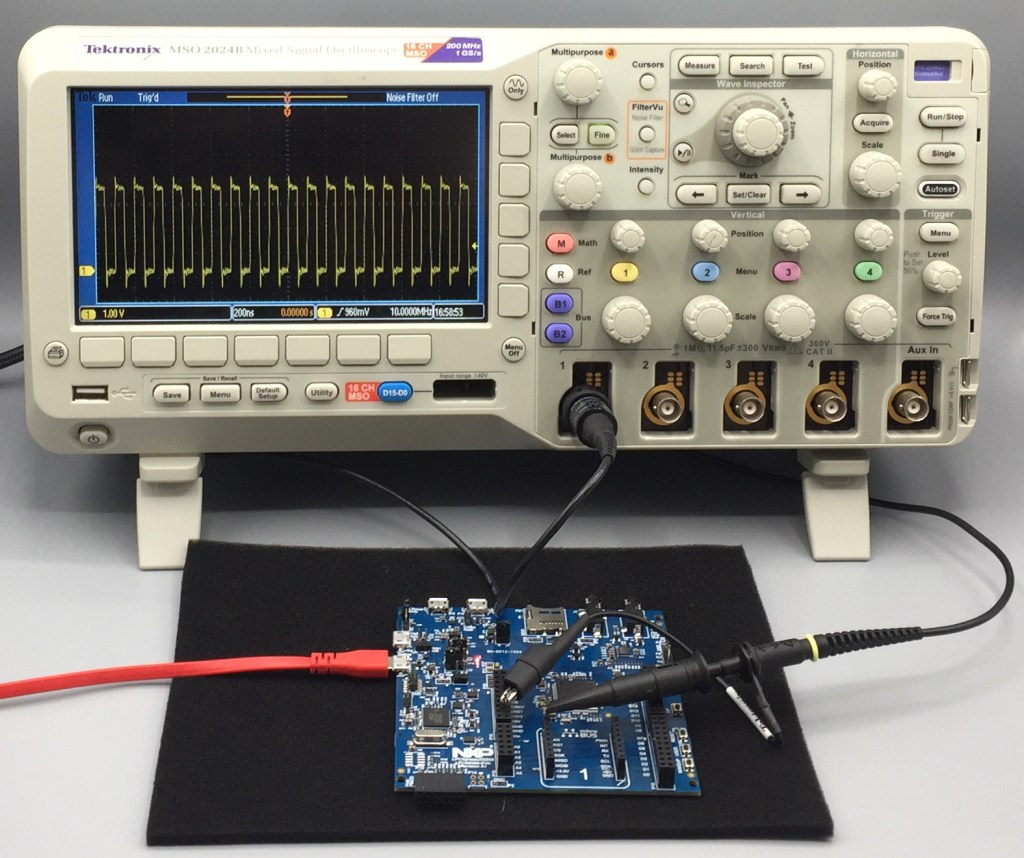
Last week I investigated the In-System Programming feature in the boot ROM of the LPC55S69. Using the command-line program blhost I was able to erase the flash and download simple LED blinky programs. Of course, the functions that erase and program the flash are present in the boot ROM.
Wouldn’t it be great if we could call those program and erase functions from our own software running on the LPC55S69?
Of course, we can. This is the NXP feature In-Application Programming, and this week I’ll show you how to interface to the Flash Driver in the boot ROM from software. Since the program and erase functions are running from ROM, this avoids the normal considerations about using flash for non-volatile storage.
Continue reading