The ‘Internet of Things’ is coming! It started as an overused marketing hype with no real use case (who needs internet connected fridges? Who wants the internet connected toilet paper?).
New ‘things’ start to pop up, useful or not: From smart bulbs (Philips Hue), thermostats (Nest), smart TV (Samsung and others) up to voice assistants (Alexa, Cortana, Google). You might even have installed one of these, right? What about temperature and humidity sensors? Probably there is nothing wrong with that?
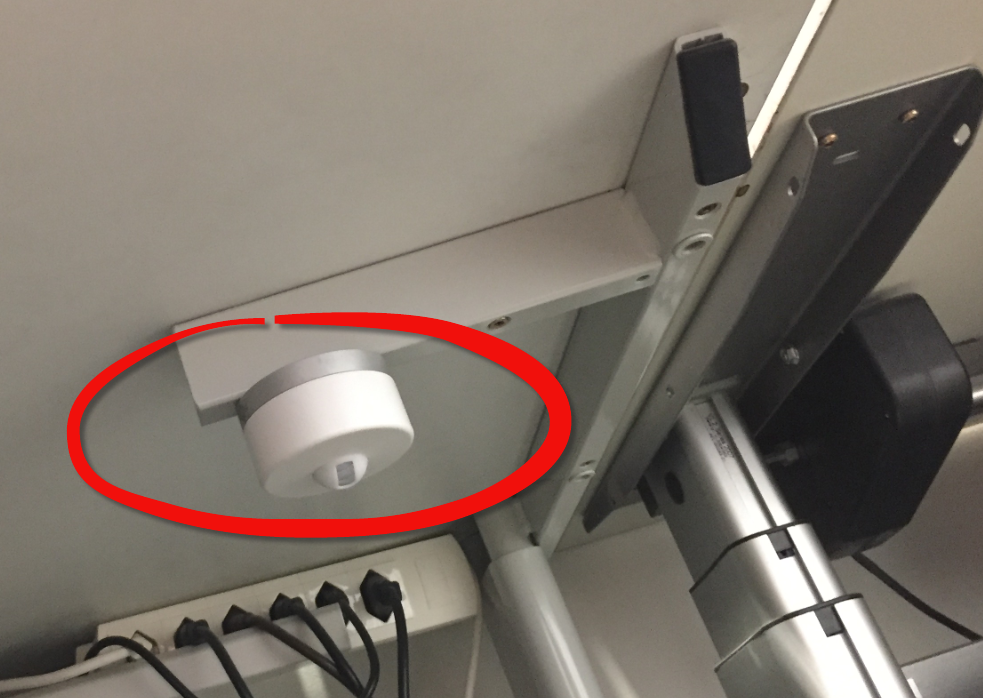
But what would you think if one morning you find a strange unknown device installed under your working desk, connected to the cloud and internet?